
Microsoft’s latest Security Intelligence Report shows that hackers have moved into weaponizing cryptocurrency miners to breach systems. Despite that, the report also shows that there has been a major decline in Ransomware and Malware attacks.
This is a significant change from previous years, following a prolific series of attacks, including NotPetya, WannaCrypt, amongst others that targeted supply chains globally. Initial predictions were that these would increase, however, improvements in cybersecurity measures and detection have impacted on the success rates of these attacks. In fact, there has been a 60% drop in Ransomware attacks globally between March and December 2018.
The report also reveals that hackers have pivoted to more covert means, with an increased focus on exploiting users through social engineering methods like phishing to gain access and exploit data. Phishing rates have increased with cybercriminals also covertly using victims’ compromised computers for Cryptocurrency Mining.
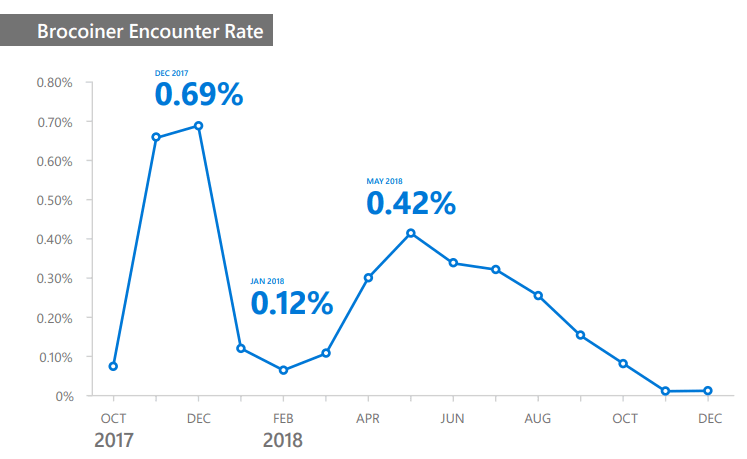
While Cryptocurrency Mining is not a new phenomenon, there has been an increase in its prevalence globally over the last year. In 2018, the average worldwide monthly Cryptocurrency coin mining encounter rate was 0.12%, compared to just 0.05% for Ransomware. Many factors contribute to the increased popularity of mining as a payload for malware. Unlike Ransomware, Cryptocurrency mining does not require user input, it works in the background, while the user is performing other tasks or is away from the computer and may not be noticed at all unless it degrades the computer’s performance sufficiently. Another driver is the availability of ‘off the shelf’ products for covert mining of many Cryptocurrencies, which cybercriminals repackage as malware to deliver to unsuspecting users’ computers.
“The decline in ransomware is good news; however, on the flip side we are seeing cryptocurrency mining to be prevalent. This is one of the methods that attackers have deployed in lieu of ransomware. Mining coins profitably requires an immense amount of computing power to perform complex calculations, so attackers install malware on users’ computers to “steal” the necessary computing power. The SIR report provides a great overview of how cryptocurrency works and other factors driving this trend,” was noted in the report.
The weaponised miners are then distributed to victims using many of the same techniques that attackers use to deliver other threats, such as social engineering exploits, and drive-by downloads. After the mining software is installed, it runs in the background on victims’ computers to perform the blockchain computations, with the attacker reaping the rewards, which grow in value as the price of the Cryptocurrency increases.
Phishing – whether through email, malvertising, or any other channel – exploits users who pay little attention to details and are likely to click on an email link or an ad, and enter sensitive information when prompted, compromising their security. The report by Microsoft noted that by adopting both public cloud tools and hosted servers, the attackers have been able to disguise themselves more easily so that they give the impression of legitimate products or services.
“While we have seen a welcome drop in ransomware and malware attacks, it would be a mistake to assume the level of cyber threat to organisations has also decreased,” said Des Ryan, Solutions Director, Microsoft Ireland. “We are seeing major behavioural change amongst criminal hackers, who want access to a victim’s computer and an organisation’s network to access data, but also use their computing power to mine for cryptocurrency. This is about playing the long game and exploiting people’s lack of training and understanding when it comes to cybercrime. Microsoft’s analysts predict phishing will continue to be an issue for the foreseeable future for that reason.”
As part of its on-going efforts to drive better security for organisations, Microsoft invests $1bn each year in security, with 3,500 full-time security professionals working at Microsoft, it analyses more than 6.5 trillion signals daily, processes 630 billion authentications monthly and scans 470 billion e-mails for malware and phishing monthly.
Tradersdna is a leading digital and social media platform for traders and investors. Tradersdna offers premiere resources for trading and investing education, digital resources for personal finance, market analysis and free trading guides. More about TradersDNA Features: What Does It Take to Become an Aggressive Trader? | Everything You Need to Know About White Label Trading Software | Advantages of Automated Forex Trading











